Security hardening
Contents
- Introduction
- Blocking invalid login attempts
- Changing the default web server port
- Enabling High Security mode
- Web interface protocols
- Password complexity
- Automatic expiry of web user passwords
Introduction
The default security settings of TIM Enterprise allow for ease of installation and are suitable for the needs of most organisations. However, if your organisation's IT security policy demands it, or you plan to expose the system to an untrusted network such as the Internet, it is recommended you harden the security using the methods described below.
info
After changing any of the following settings, you will need to restart the TIM Enterprise service for the changes to take effect.
Blocking invalid login attempts
The system can blacklist the source IP address of a would-be attacker if a number of unsuccessful access attempts are made within a specified period of time. The following two Registry entries determine how many invalid login attempts are permissible before the source IP is blacklisted and, if so, for how long the blacklist will remain in place until further attempts are entertained:
| Registry String data value | Description |
|---|---|
| FloodFailCount = 0 | Number of attempts |
| FloodLockTime = 60 | Lockout duration |
All Registry keys for TIM Enterprise are located in the following hive:
HKEY_LOCAL_MACHINE\SOFTWARE\Tri-Line\TIM Enterprise
Changing the default web server port
If you would like to change the default port used for web traffic, you can edit the WWWServerPort Registry key.
| Registry String data value | Description |
|---|---|
| WWWServerPort = port number | Port address for webserver to listen on (Default is 80, unless changed during setup) |
Enabling High Security mode
To enable High Security mode, add the following Registry String value:
HKEY_LOCAL_MACHINE\SOFTWARE\Tri-Line\TIM Enterprise\Main\HighSecurity = "True"
Within the Windows Registry, right click and select New -> String Value and name it HighSecurity.
Next, double-click on it and enter the Value of True, as shown below:
When the HighSecurity Registry value is set to True, the following restrictions are imposed:
- Ability to block individual web scripts by including them in a blacklist file:
"\ssldata\{class}\blacklist.___"
Enforce password complexity for web users (additional Registry entries required)
Forbid direct SQL queries through web interface
System alert messages are silently suppressed
System database connection tests forbidden
Ability to (re)create system database tables inhibited
Cannot change or test web (HTTP) port
Cannot send test emails
Debug information suppressed if a XSL translation error occurs
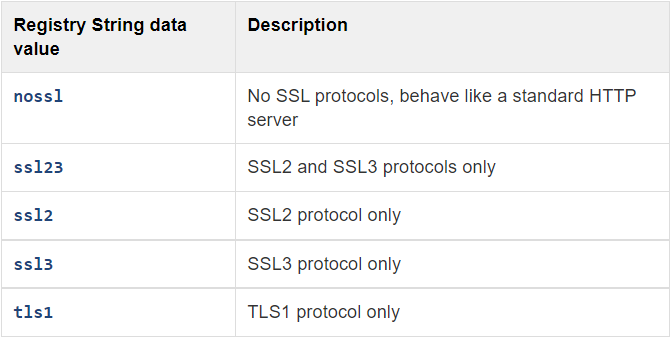
Web interface protocols
The default behaviour is to allow all protocols TLS1, SSL2 and SSL3.
You can change the type of connection that TIM will respond to, by adding the Registry String Value WWWSSLProtocol.
Note that this is a case-insensitive string value with one of the following data values:
Password complexity
You can configure TIM Enterprise web users with complex passwords to match your organisation's IT password policy.
To enable complex passwords, a Registry String Value PasswordComplexity must be added.
The use of the following data string values, allows you to configure how complex the passwords are:
"A"+{0-9}+"a"+{0-9}+"!"+{0-9}+"#"+{0-9}
Each part of the complexity string is defined by a pair of characters, a single character denoting the type of policy, immediately followed by a numeric character (0-9) stipulating how many characters of that type are required to satisfy the password policy.
The Type characters are as follows:
A: Upper- or lower-case characters a: Lower-case characters !: Symbol characters #: Numeric characters
For example, to impose a restriction of at least 6 characters with two numbers, the following Registry entry could be used:
HKEY_LOCAL_MACHINE\SOFTWARE\Tri-Line\TIM Enterprise\Main\PasswordComplexity = "A6a0!0#2"
info
The value of PasswordComplexity must always be 8 characters, otherwise the policy will not be implemented. The order of each Type pair ( Type character and amount character) is not important.
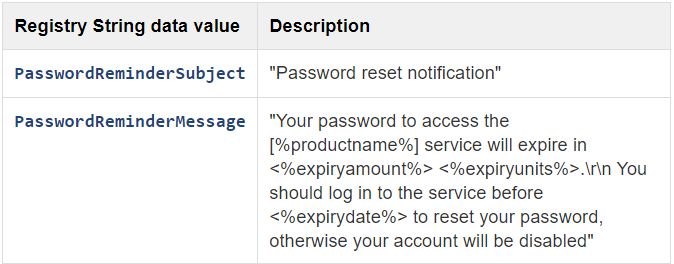
Automatic expiry of web user passwords
You can force Web users to change the password after a predetermined age has been set. Note that this is a system wide setting.
The server running TIM Enterprise will email the web user advising that a password change is required. The web user must have an email address configured, for notification to take place.
If the password is not changed by the expiry date, the account is automatically disabled.
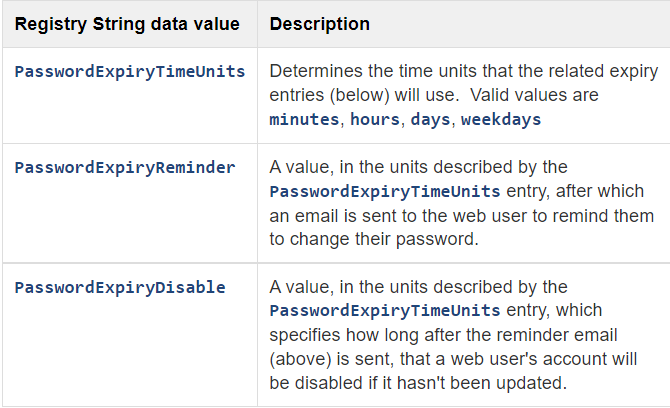
Default values for the above settings are as follows:
- PasswordExpiryTimeUnits = "days"
- PasswordExpiryReminder = "7"
- PasswordExpiryDisable = "7"
Therefore, using the default settings, a web user will receive an email reminder after 7 days and the account will be disabled after 14 days.
If the PasswordExpiryReminder value is zero then password reminder functionality is disabled and neither a reminder email will be sent, nor will a web user's account be disabled. Since this value has a default of "7", this value must be explicitly set to zero to disable password reminder functionality.
If the PasswordExpiryDisable value is explicitly set to zero, the disabling of a web user's account is skipped.
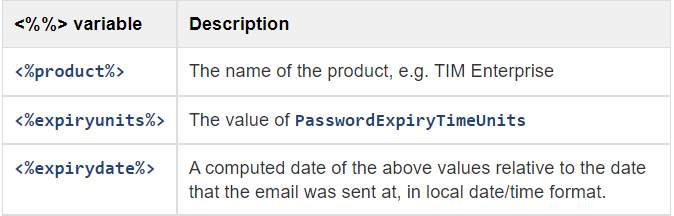
The following <%%> variables are permissible in both the subject and the body text of the reminder email message: